How to update Edge Firewall
Previously, to use a rule set from Edge Firewall or Web Application Firewall (WAF), you had to activate these modules in the Main Settings tab of each edge application. Then, criteria and behaviors were applied in the application’s Rules Engine tab.
Azion Edge Firewall has evolved into an independent product including all security functionalities: DDoS Protection, Network Layer Protection, Web Application Firewall, and Edge Functions. This update facilitates the creation of new security policies that can be applied globally or specifically. Consequently, rule sets used in deprecated versions of Edge Firewall have also been deprecated.
This documentation will guide you through updating the Edge Firewall features used in the deprecated versions to the latest ones. Each section describes how each feature works on the new modules, Network Lists, and Rules Engine.
Go to Edge Firewall referenceCreating new rules in Edge Firewall
First, you must create an edge firewall to add new rules based on the pre-existing rules later.
- Access Azion Console > Edge Firewall.
- Create a new edge firewall by clicking the + Edge Firewall button.
- Alternatively, you can edit an already created one.
- Follow the steps explained below according to the functionality.
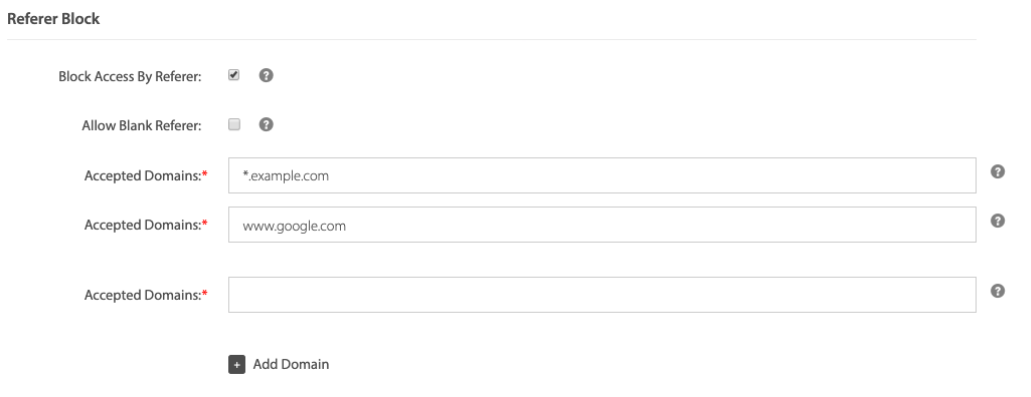
Referrer Block
If you used Referer Block in your deprecated rule set, still in the new edge firewall:
- In the Main Settings tab, enable the Web Application Firewall module.
- Click the Save button.
- Go to the Rules Engine tab.
- Click the + Rule Engine button.
- Give a name and, optionally, a description for your rule.
- In the Criteria section, set the desired criteria to trigger the rule:
- If
Header Refererdoes not matchyourdomain.com. - Use the accepted domain of the old rule set.
- If
- For each domain in Accepted Domains of the old rule set, click the + Add Criteria button and repeat the step 6.
- In the Behavior section, select Deny (403 Forbidden).
- Click the Save button.
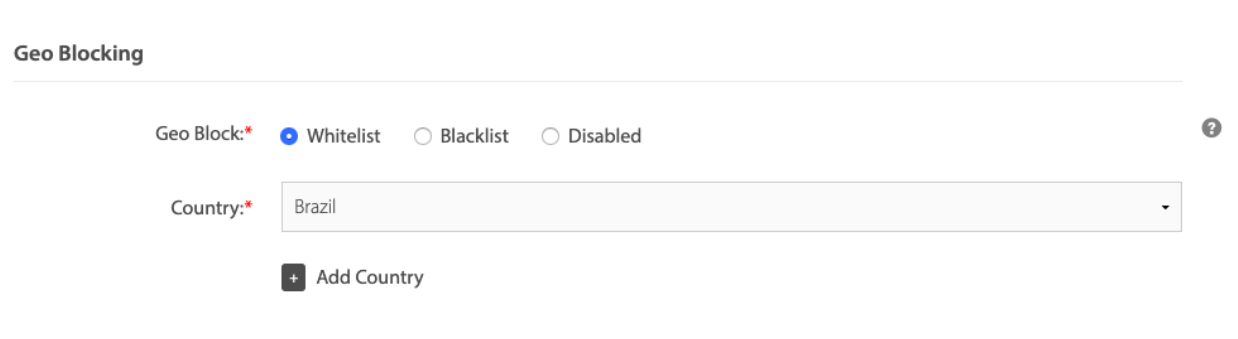
Geo-Blocking
If you used Geo-Blocking in your deprecated rule set:
- Access Azion Console > Network Lists.
- Create a new network list by clicking the + Network List button.
- Alternatively, you can edit an already created one.
- Give a name for your network list.
- In Type, select Countries.
- In the Countries dropdown, select the countries you want to add, based on the the deprecated rule set.
- Click the Save button.
Now it’s time to create a rule using the network list for your edge firewall:
- Go to Products menu > Edge Firewall.
- Select the firewall you created previously.
- In Main Settings, enable the Network Layer Protection module.
- Click the Save button.
- Go to the Rules Engine tab.
- Click the + Rule Engine button.
- Give a name and, optionally, a description for your rule.
- In the Criteria section, set the desired criteria to trigger the rule:
- If
Networkdoes not matchyour network list(to use as an allowlist) or IfNetworkmatchesyour network list(to use as a blocklist). - Select the network list you created in the previous steps as the value.
- If
- In the Behavior section, select Deny (403 Forbidden).
- Click the Save button.
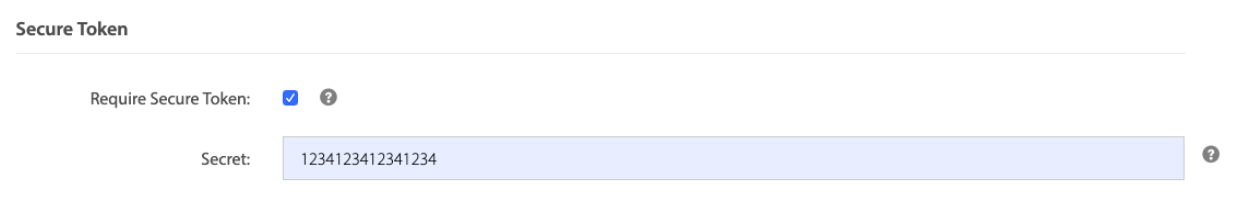
Secure Token
If you used Secure Token in your deprecated rule set, still in the new edge firewall:
- In the Main Settings tab, enable the Edge Functions module.
- Click the Save button.
- Go to the Functions Intances tab.
- Click the + Function Intance button.
- Give a name for your instance.
- In Edge Function, select the Secure Token function.
- Use the Arguments box to define the secret that composes the hash.
- Click the Save button.
- Go to the Rules Engine tab.
- Click the + Rules Engine button.
- Give a name and, optionally, a description for your rule.
- In the Criteria section, set the desired criteria to trigger the rule.
- For example: if
Hostis equalxxxxxxxxxxxx.map.azionedge.net/classes.
- In the Behavior section, select Run Function.
- In the dropdown, select the function instance you created to Secure Token.
- Click the Save button.
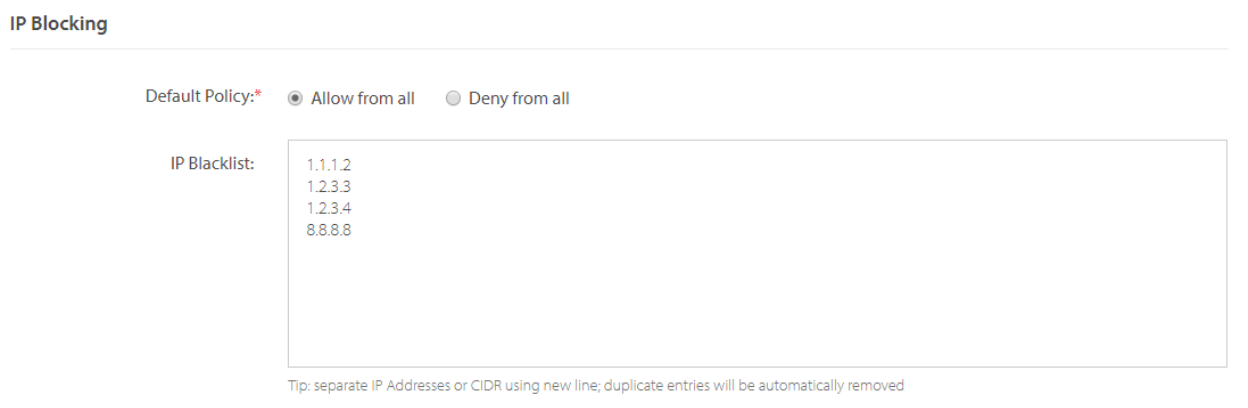
IP Blocking
If you used IP Blocking in your deprecated rule set:
- Access Azion Console > Network Lists.
- Create a new network list by clicking the + Network List button.
- Alternatively, you can edit an already created one.
- Give a name for your network list.
- In Type, select IP/CIDR.
- In the List box, copy the list of blocked IPs from the deprecated rule set.
- Click the Save button.
Now it’s time to create a rule using the network list for your edge firewall:
- Go to Products menu > Edge Firewall.
- Select the firewall you created previously.
- In Main Settings, enable the Network Layer Protection module.
- Click the Save button.
- Go to the Rules Engine tab.
- Click the + Rule Engine button.
- Give a name and, optionally, a description for your rule.
- In the Criteria section, set the desired criteria to trigger the rule:
- If
Networkdoes not matchyour network list(to use as an allowlist) or IfNetworkmatchesyour network list(to use as a blocklist). - Select the network list you created in the previous steps as the value.
- If
- In the Behavior section, select Deny (403 Forbidden).
- Click the Save button.
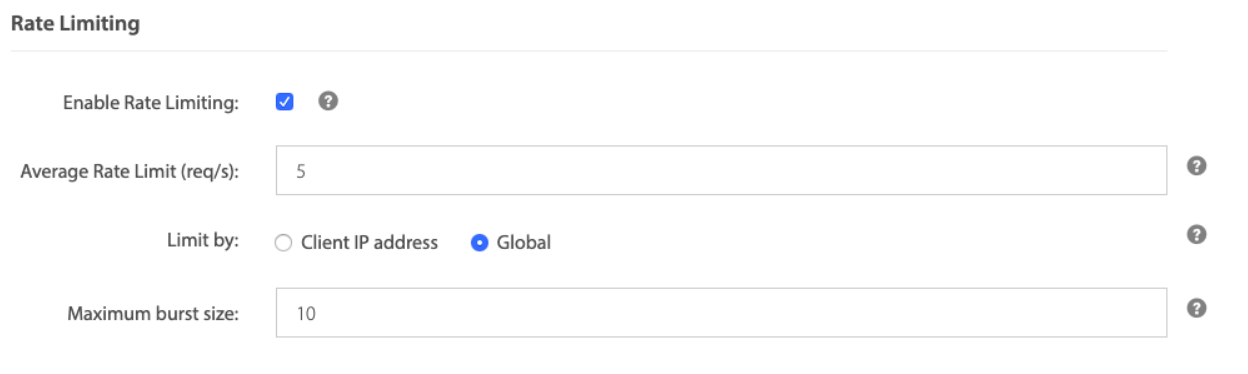
Rate Limiting
If you used Rate Limiting in your deprecated rule set, still in the new edge firewall:
- Go to the Rules Engine tab.
- Click the + Rule Engine button.
- Give a name and, optionally, a description for your rule.
- In the Criteria section, set the desired criteria to trigger the rule.
- In the Behavior section, select Set Rate Limit.
- In the Rate Limit type, select either Req/s or Req/min and define the average rate limit.
- Select if you want to set a limit by Client IP Address or Global and the maximum burst size.
- Click the Save button.
Domains association
You can also associate one or more domains with the new edge firewall:
- Access Azion Console > Edge Firewall.
- Select the firewall you created previously.
- In the Main Settings tab, go to the Domains section.
- Select each domain you want to associate with this firewall and click the
>button. - Select multiple domains by using
ctrlon Windows and Linux orcommandon Mac and click the>button. - Select
>>to select all domains presented on the Available list.
- Select each domain you want to associate with this firewall and click the
- Click the Save button.
WAF Rule Set Association
You can also associate one or more WAF Rule Sets with the new edge firewall:
- Access Azion Console > Edge Firewall.
- Select the firewall you created previously.
- In the Main Settings tab, enable the Web Application Firewall module.
- Click the Save button.
Now it’s time to create a rule using the WAF Rule Set for your edge firewall:
- Go to the Rules Engine tab.
- Click the + Rule Engine button to add a new rule or edit an existing one.
- Give a name and, optionally, a description for your rule.
- In the Criteria section, set the desired criteria to trigger the rule.
- In the Behavior section, select Set WAF Rule Set and choose a WAF Rule Set.
- Click the Save button.
Removing the Edge Firewall rules in your edge application
After creating and applying the rule for the latest version of Edge Firewall for your domain, you must remove the rules in your edge application:
- Access Azion Console > Edge Application.
- Select the edge application with the deprecated configurations.
- In the Rules Engine tab, select any rule including the behaviors Set Edge Firewall with Rule Sets or Set WAF Rule Set.
- Remove the behavior by clicking the trash can icon and your rule will be removed.
- To remove the whole rule, in the list, click the three points in the right corner of the rule and select the Delete option. Then, confirm the deletion in the modal and your rule will be removed.
- Click the Save button.