KV Store
Preview
Store and access data with low global latency using a distributed, serverless KV store.
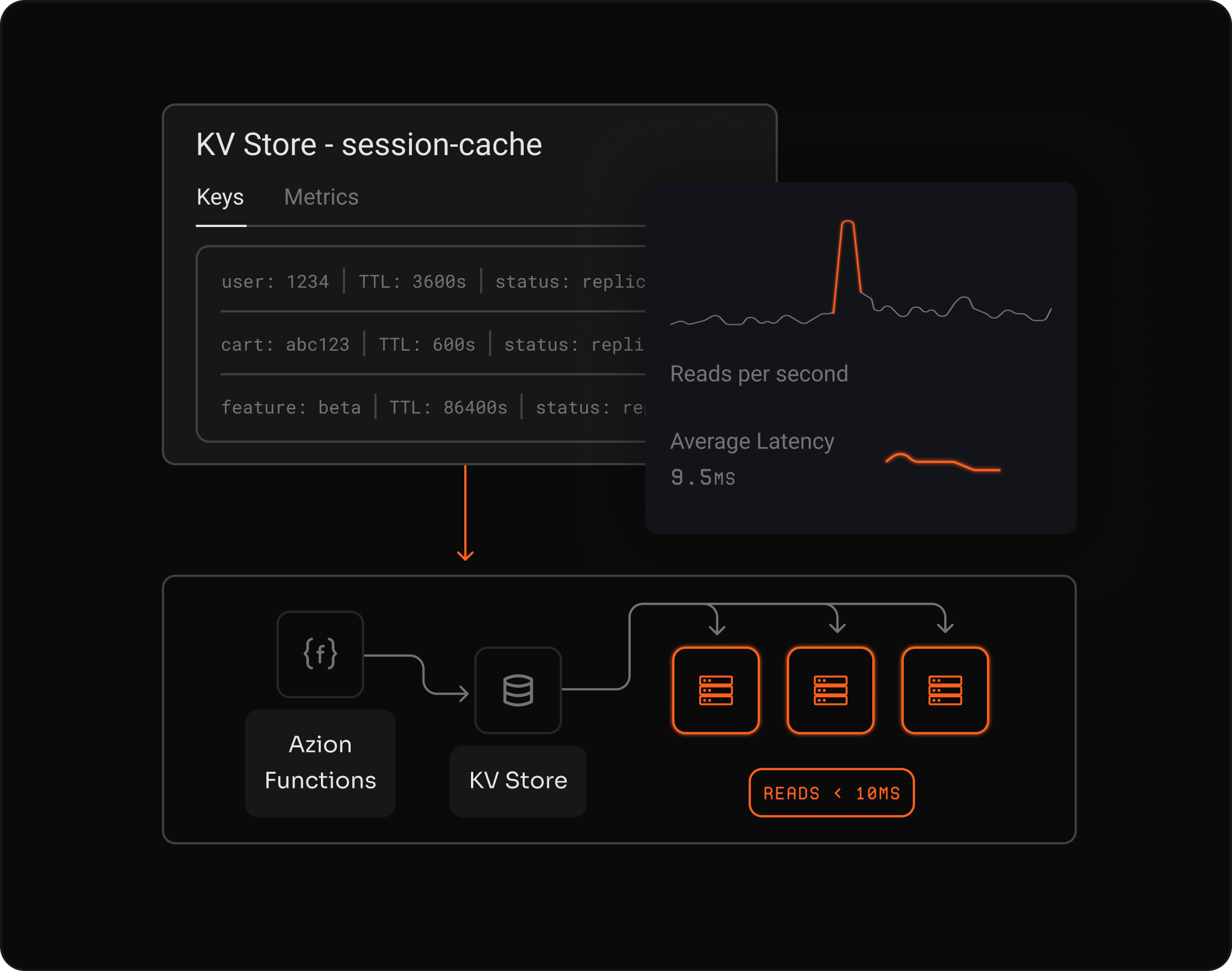
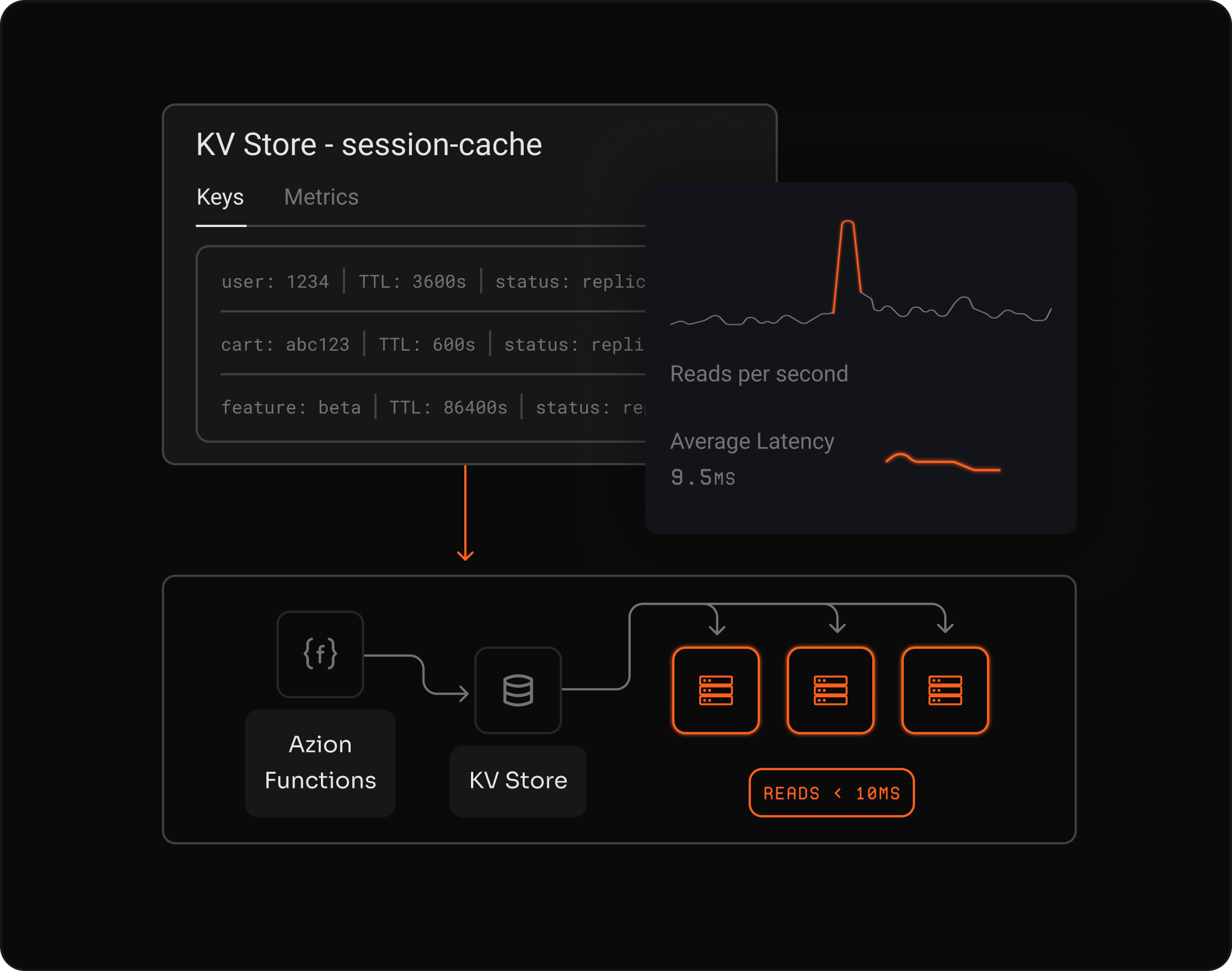
Reduce global latency
Reads close to users on a distributed architecture. A low-latency KV Store for flags, sessions, and counters.
Scale without managing servers
Automatic scaling, simple APIs and direct integration with Functions and applications.
Ensure consistency with distributed replication
A primary instance handles writes while global replicas ensure high availability.












"The partnership with Azion allowed us to guarantee security and performance, from an endpoint connection to the connection of our servers with high availability, and it has brought us great benefits."
Diego Romano
Computer Security Incident Response Team (CSIRT) at Pernambucanas
Native JavaScript API for Functions
Access KV Store directly from Functions to store and retrieve sessions, flags, and counters without extra network hops.
Native JS API Functions integration TTL support Zero network hops
Store any data type, no schema required
Store JSON, binary data, and streams without rigid schemas, with support for metadata and multiple formats.
JSON objects Binary buffers Streams Metadata
See how to use
Frequently Asked Questions
What is KV Store?
Azion KV Store is a serverless key-value storage with global read replicas. Key features include: sub-10ms read latency, automatic replication to 100+ locations, native Functions integration, TTL support, and flexible data types (String, JSON, Buffer, Stream). Ideal for sessions, feature flags, and rate limiting.
What data types does KV Store support?
KV Store supports 4 data types: String, JSON, buffers, and streams. The schemaless design allows flexible data modeling without rigid schemas.
How does replication work?
KV Store uses a primary instance for writes and global read replicas. Data synchronizes with eventual consistency, providing high availability and low-latency reads close to users.
Can I set expiration on keys?
Yes. KV Store supports native TTL (time-to-live) to automatically expire ephemeral keys and short-term configurations.
How do I access KV Store from Functions?
Functions can access KV Store through a native JavaScript API in the runtime. This enables direct integration without extra network hops.
What are common use cases for KV Store?
Common use cases include user sessions and authentication tokens, feature flags and configuration management, API rate limiting and quotas, and global counters for analytics.
What are the storage limits?
KV Store supports keys up to 512 bytes and values up to 25 MB. You can also attach metadata to each key-value pair for additional context.
Is KV Store compatible with Cloudflare Workers KV?
Yes. KV Store provides a compatible API with Cloudflare Workers KV, making it easier to migrate existing applications or use familiar patterns.
Is there a free tier to test KV Store?
Yes. You get $300 in credits valid for 365 days to start testing KV Store and other Azion products.
Access to all features.