Let’s Encrypt: Obtaining SSL Certificates with ACME Protocol
Let’s Encrypt is a free, open, and automated Certificate Authority (CA) used to issue SSL certificates using the ACME (Automatic Certificate Management Environment) protocol. SSL certificates are a crucial component for Web Application Security and the success of a website, as they enable secure data transfer using HTTPS. Not only does HTTPS increase a site’s search engine positioning and users’ trust, it enables use of the HTTP/2 protocol, resulting in significant performance improvements over HTTP/1.
To use their own HTTPS domain, users can upload their own SSL certificate. However, in order to obtain an SSL certificate, users must use a CA like Let’s Encrypt to validate the server’s identity and issue a certificate that binds the identity to the server’s public key. This article will walk readers through the process, from installing and configuring the necessary software to emitting certificates through both HTTP and DNS challenge types.
What is ACME and How Does It Work?
Let’s Encrypt uses the ACME (Automatic Certificate Management Environment) protocol to check if you control a given domain name and to emit a certificate. With ACME, the process of obtaining an SSL certificate is fully automated, which improves security by reducing the possibility of error and enables Let’s Encrypt to offer domain-validated certificates for free.
ACME allows software agents on HTTPS servers to obtain, provision, and renew certificates automatically, with no human interaction. However, before the requesting client can manage the certificate, they must first prove that they control the domain. First, the requesting agent sends the public key for their server and asks the Let’s Encrypt CA what needs to be done to prove it controls the domain. The CA will then provide a list of challenges the client can complete to validate control of the domain and a token, which the client must sign with its private key pair.
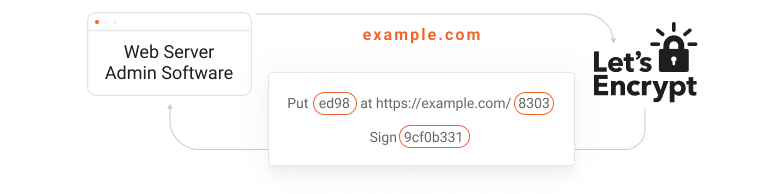
After the client completes the challenges, the client signs the token with its private key to prove it controls the key pair and notifies the CA that they are ready to complete validation. Once the CA ensures that the challenge is complete and verifies the signature, the agent is authorized for certificate management using the key pair.
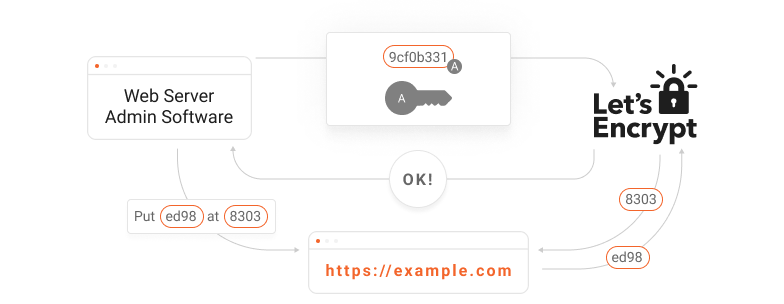
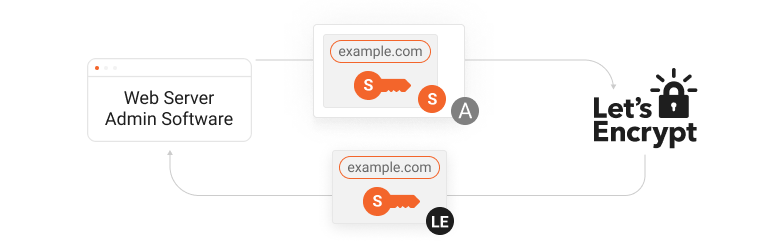
To obtain a certificate, the agent constructs a PKCS#10 Certificate Signing Request (CSR) asking the CA to issue a certificate for the domain using a specified public key, accompanied by the signature of the corresponding private key and the signature of the authorized key pair for the domain. After verifying both signatures, The CA issues a certificate for the domain with the public key from the CSR.
Installation and Configuration of acme.sh
To obtain a Let’s Encrypt certificate, you’ll need to choose an ACME client software. One of the ACME client softwares recommended and maintained by the community is acmesh, which implements ACME protocol in pure Unix shell script and therefore is supported on multiple platforms (such as Mac OSX, Windows, FreeBSD, Solaris and many Linux distributions).
By using acme.sh, it is possible to emit and renew certificates using both HTTP and DNS challenge types. Acme.sh is IPv6 ready and easy to use. Although GitHub provides additional installation methods, this tutorial will walk you through installation and configuration via curl command.
Acme.sh can be installed on the same origin server as your application or on a server reserved to run this service. The curl command for installation is:
curl https://get.acme.sh | sh -s email=your.email@example.comsource ~/.bashrcInstallation can be verified by issuing the command:
acme.sh --versionv2.8.1After acme.sh is installed, you can configure it to use Let’s Encrypt as a CA (Certificate Authority) with the command:
acme.sh --set-default-ca --server letsencryptCompleting Challenges
Once acme.sh is installed and configured, you can use it to prove control of your domain using one of the challenges specified by the CA, such as provisioning an HTTP resource under one of the domain’s well-known URIs or provisioning a DNS record under the domain. Although HTTP is the most common challenge type, you may wish to use the DNS method if you are issuing certificates for a wildcard domain or have multiple web servers.
HTTP Challenge
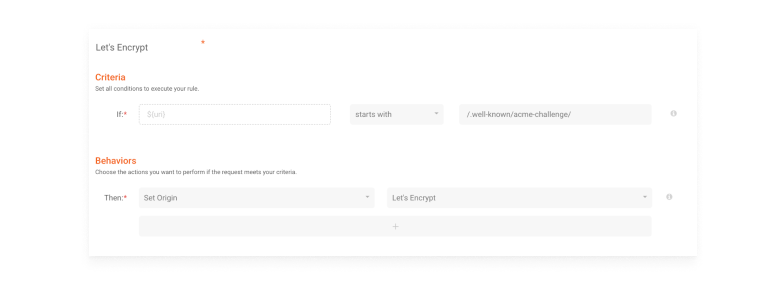
This is currently the most common challenge type, as it is easy to automate and works well with off-the-shelf web servers. Let’s Encrypt provides the client with an ACME token, and it must insert a file on your web server on http://<YOUR_DOMAIN>/.well-known/acme-challenge/<TOKEN>
If you’re running acme.sh on a different server than your main origin, you just need to set a rule to direct this path’s requests to that server.
The certificate generation can be done with a single command:
acme.sh --issue -d lets.httpbin.xyz -w /usr/share/nginx/htmlAfter this command, it takes less than 10s to complete the challenge process.
Acme.sh will store the file on the indicated location (/usr/share/nginx/html) and both your edge application and your origin server will receive a request to obtain this file. If the process is finished successfully, acme.sh will show the certificate files location, key and strings.
DNS Challenge
The ACME challenge using DNS adds a specific value to a TXT record on your domain’s DNS. Typically, this challenge type is harder to configure than HTTP, but if your domain is set up on a DNS service with API access, this process can be made extremely fast using acme.sh.
However, keeping API credentials on your web server increases the impact of an attack if that web server is hacked. Therefore, for security reasons, we recommend you to create an account configured exclusively for this integration, with permissions to the DNS service only.
To integrate acme.sh with a DNS API, you need to set up the appropriate environment variables for access authentication. The exact variables will depend on your DNS provider.
For example, if you are using a DNS provider with API access:
export DNS_API_Email="your.email@example.com"export DNS_API_Password="<YOUR PASSWORD>"The certificate can then be generated using the following command (replace dns_provider with your actual DNS provider’s acme.sh module name):
acme.sh --issue --dns dns_provider -d example.comThis whole process can be followed by logs. acme.sh will access the DNS API and add the record (TXT _acme-challenge.example.com) to the chosen domain. After that, Let’s Encrypt will make a record query, and if everything is working properly, the certificate and keys are provided.
Now you just have to upload the content of your certificate and keys to your web server or content delivery platform to use them with your domain.
Conclusion
With a rise in both the cost and frequency of cyberattacks over the past year, it’s more important than ever that digital business owners commit to the security of their websites by obtaining SSL certificates for their domains. Although this process was once cumbersome, expensive, and prone to human error, Let’s Encrypt has dramatically increased the adoption of HTTPS since its launch by significantly reducing the financial and procedural burden of certificate management.
By following this process, users can easily obtain SSL certificates and, using DNS API integration, even complete DNS challenges for specialized use cases in a manner that is both simple and secure.