Application and API protection you can control and trust
Stop emerging threats globally without slowing your applications.






















Zero-day defense
Block zero-day exploits and emerging threats with rules you don't need to update.
Global performance
Azion uses globally distributed infrastructure to keep your applications secure and fast.
Low false positives
Security rules that can automatically adapt to your application to stop only malicious traffic.
Distributed protection across every request













"Azion shielded us from sophisticated cyberattacks and empowered us to modernize our infrastructure, reduce costs, and deliver the best shopping experiences to millions of customers across Latin America."
Allan Monteiro
CISO & Head of Technology
Protect critical applications and APIs
Frequently Asked Questions
What is a WAF and how does it work?
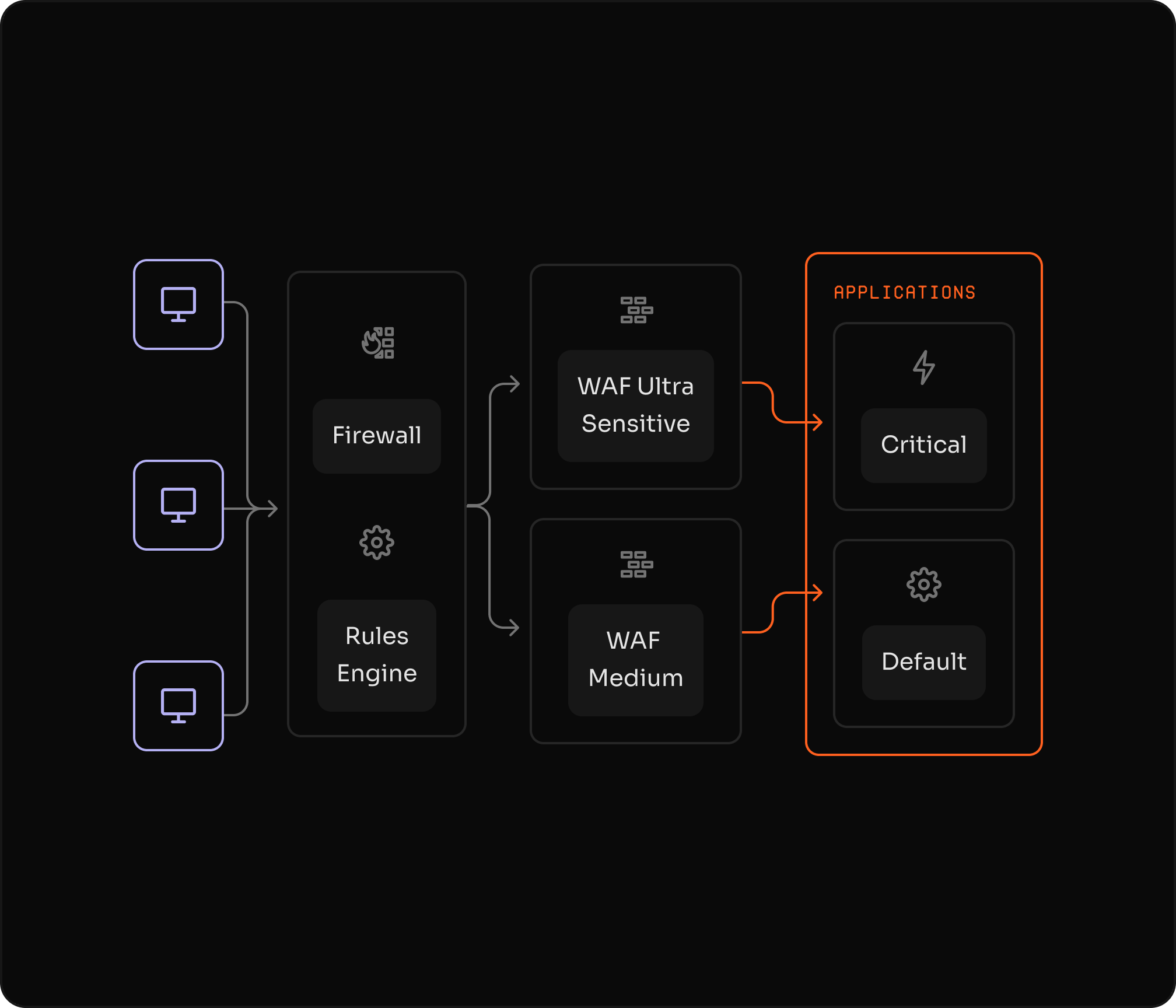
A WAF (Web Application Firewall) monitors, filters, and blocks HTTP/HTTPS traffic at Layer 7. It analyzes each request against security rules to detect and block threats like SQL injection, cross-site scripting (XSS), and OWASP Top 10 attacks before they reach your origin servers.
I'm under attack. What should I do?
Your system is under attack right now? Get immediate expert help.
What happens next:
- Connect with our security specialists instantly
- Real-time attack analysis and threat identification
- Custom security rules deployed to block the attack
- Advanced protection activated immediately
Don't wait - every second counts during an active attack.
Can I use WAF alongside my existing security tools?
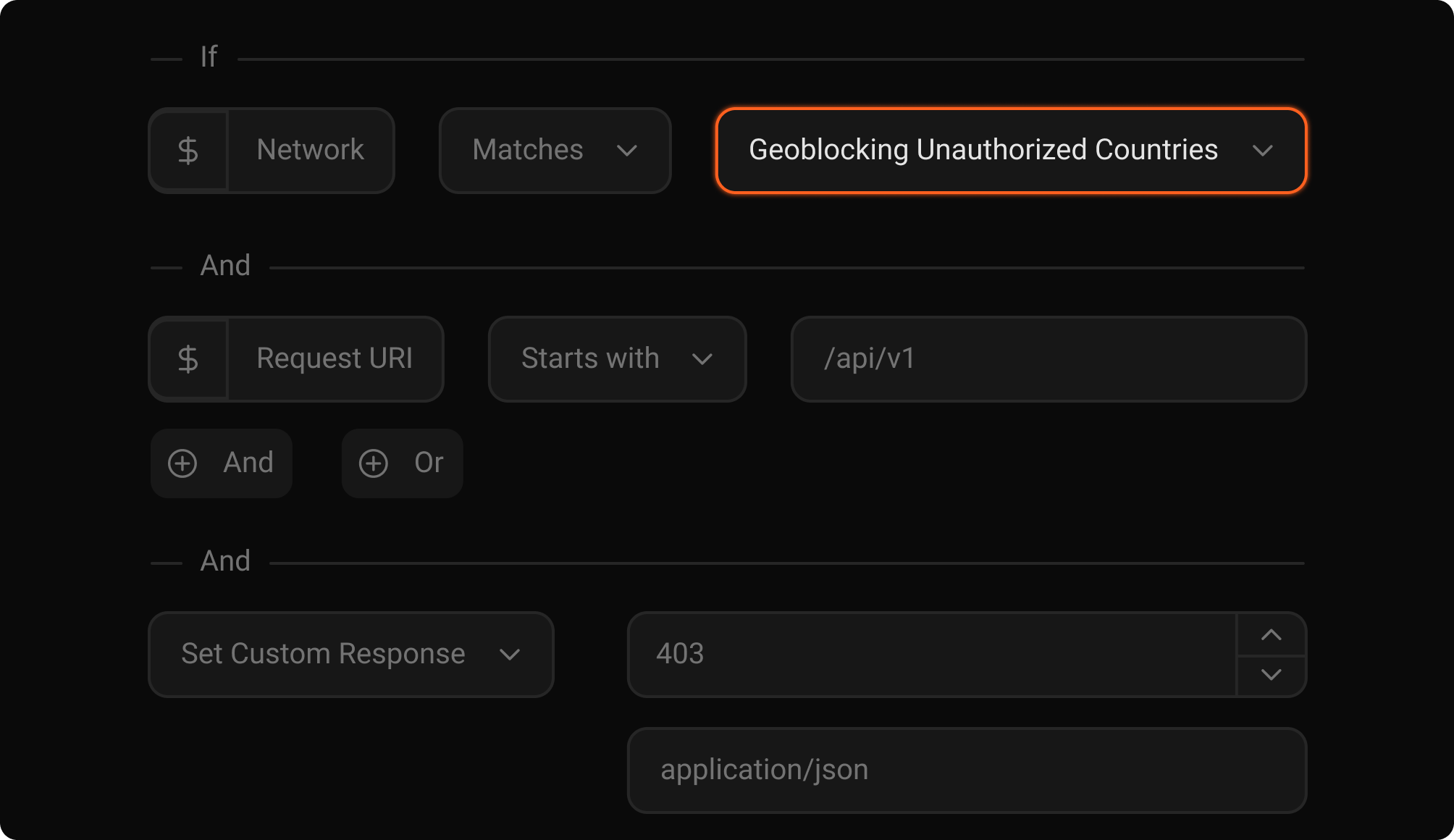
Yes. Azion WAF integrates with your existing security stack and can be deployed alongside CDNs, load balancers, and other security solutions. Unlike standalone WAFs, Azion operates as part of a unified security platform—combine WAF with Bot Manager, Network Shield, and custom Functions for comprehensive protection. Stream security events to your SIEM via Data Stream for centralized visibility across all tools.
What is the difference between a WAF and a traditional firewall?
Traditional firewalls operate at the network layer (Layer 3-4) and filter traffic based on IP addresses, ports, and protocols. A WAF operates at the application layer (Layer 7) and understands HTTP/HTTPS protocols, analyzing request content, headers, cookies, and payloads to detect application-specific attacks. While network firewalls protect infrastructure, WAFs specifically protect web applications from threats like SQL injection, XSS, and zero-day exploits that traditional firewalls cannot detect.
How long does it take to deploy and implement a WAF?
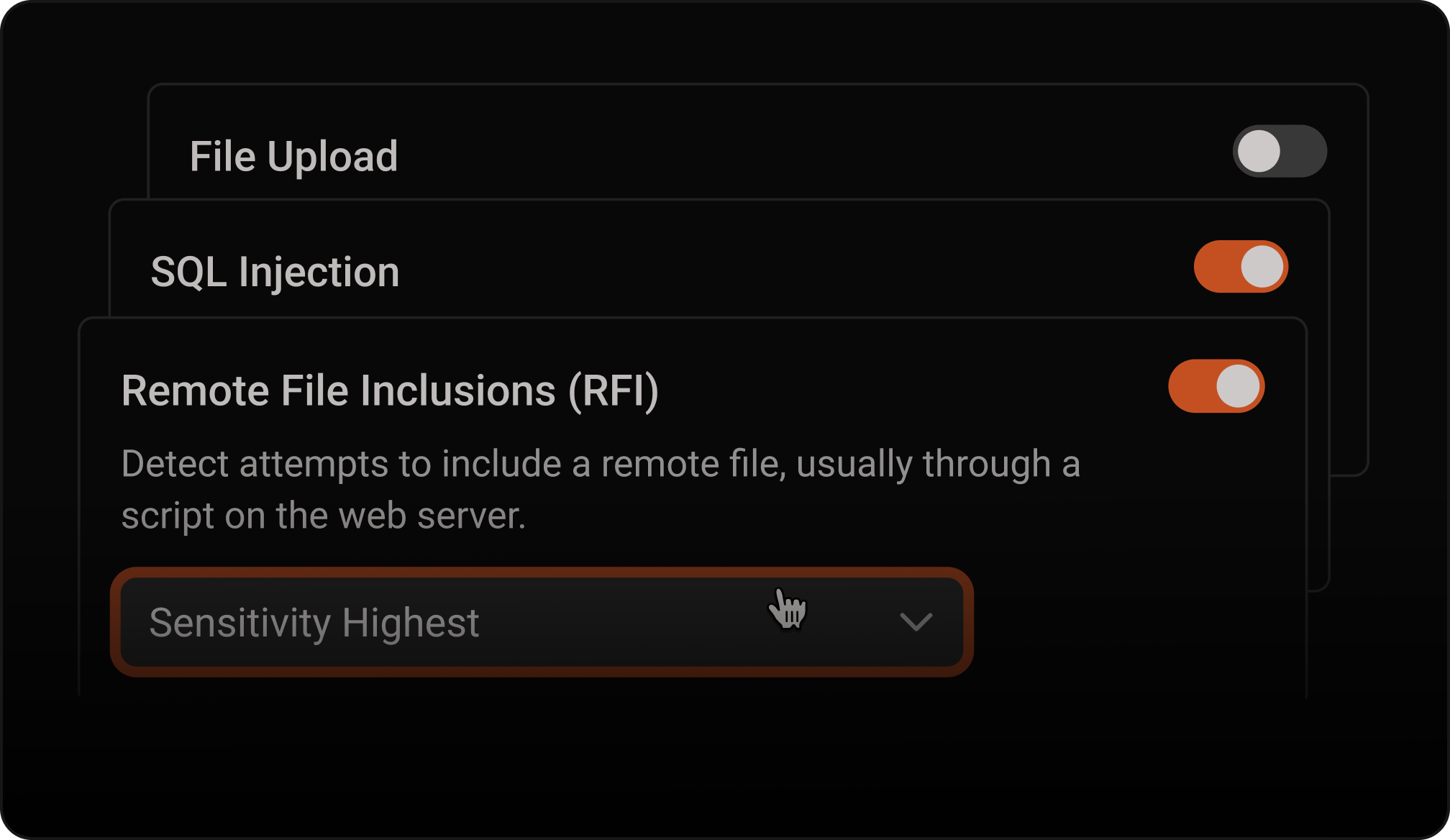
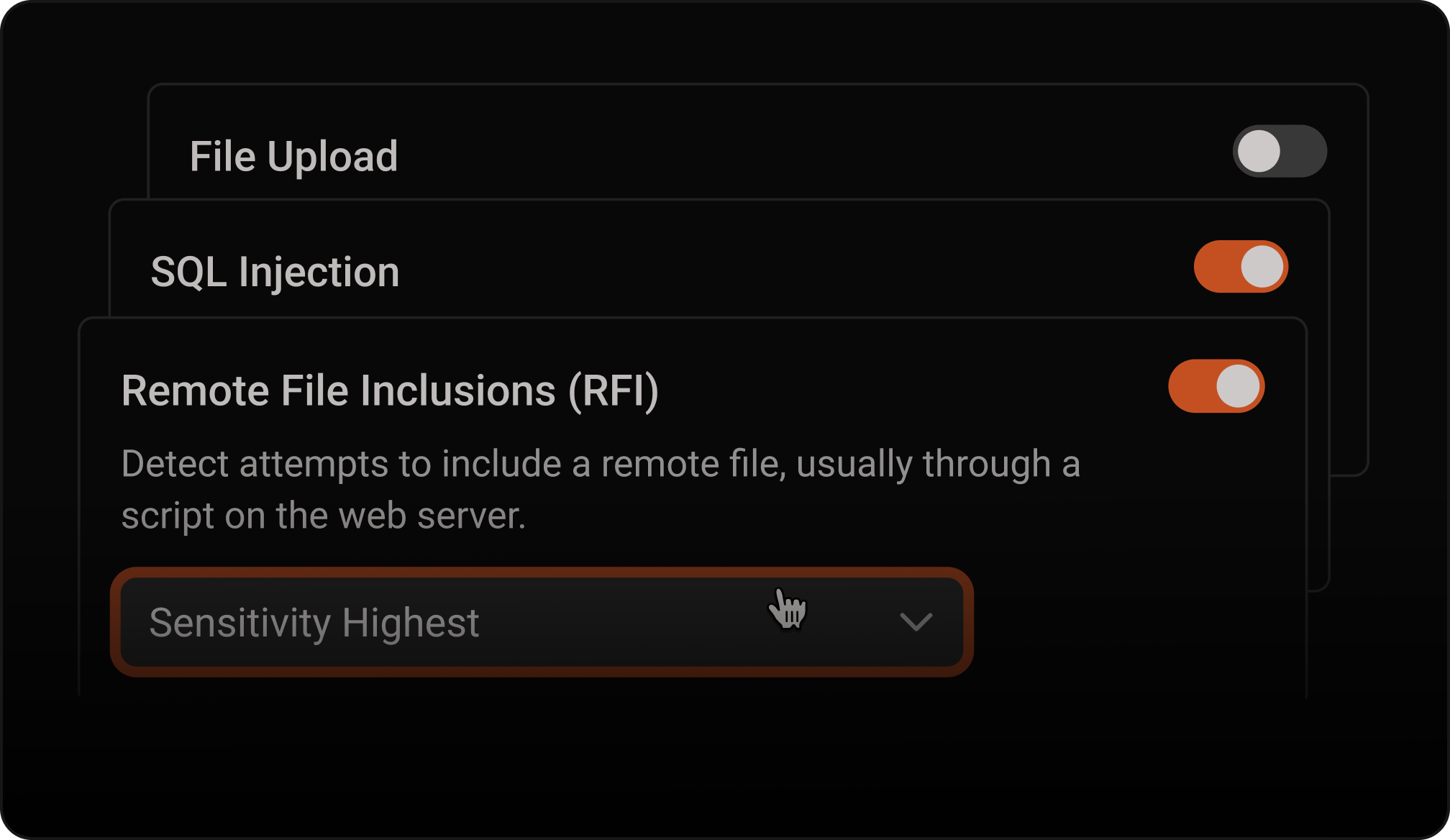
Azion WAF can be deployed in under 30 minutes with no hardware provisioning or complex setup required. Simply configure your DNS to point to Azion's network, enable WAF protection in the console, and select your security rules. Start in Learning Mode to observe traffic patterns, tune sensitivity levels to eliminate false positives, then switch to Blocking Mode. Unlike traditional WAF solutions that take weeks or months to implement, Azion WAF provides immediate protection with minimal configuration.
Does Azion WAF protect against OWASP Top 10 vulnerabilities?
Yes, Azion WAF provides comprehensive protection against all OWASP Top 10 threats including SQL injection, cross-site scripting (XSS), broken authentication, sensitive data exposure, XML external entities (XXE), broken access control, security misconfigurations, cross-site request forgery (CSRF), insecure deserialization, and components with known vulnerabilities. Our rule sets are continuously updated with the latest threat intelligence and zero-day vulnerability signatures to protect against emerging attacks.
What types of attacks can Azion's security platform prevent?
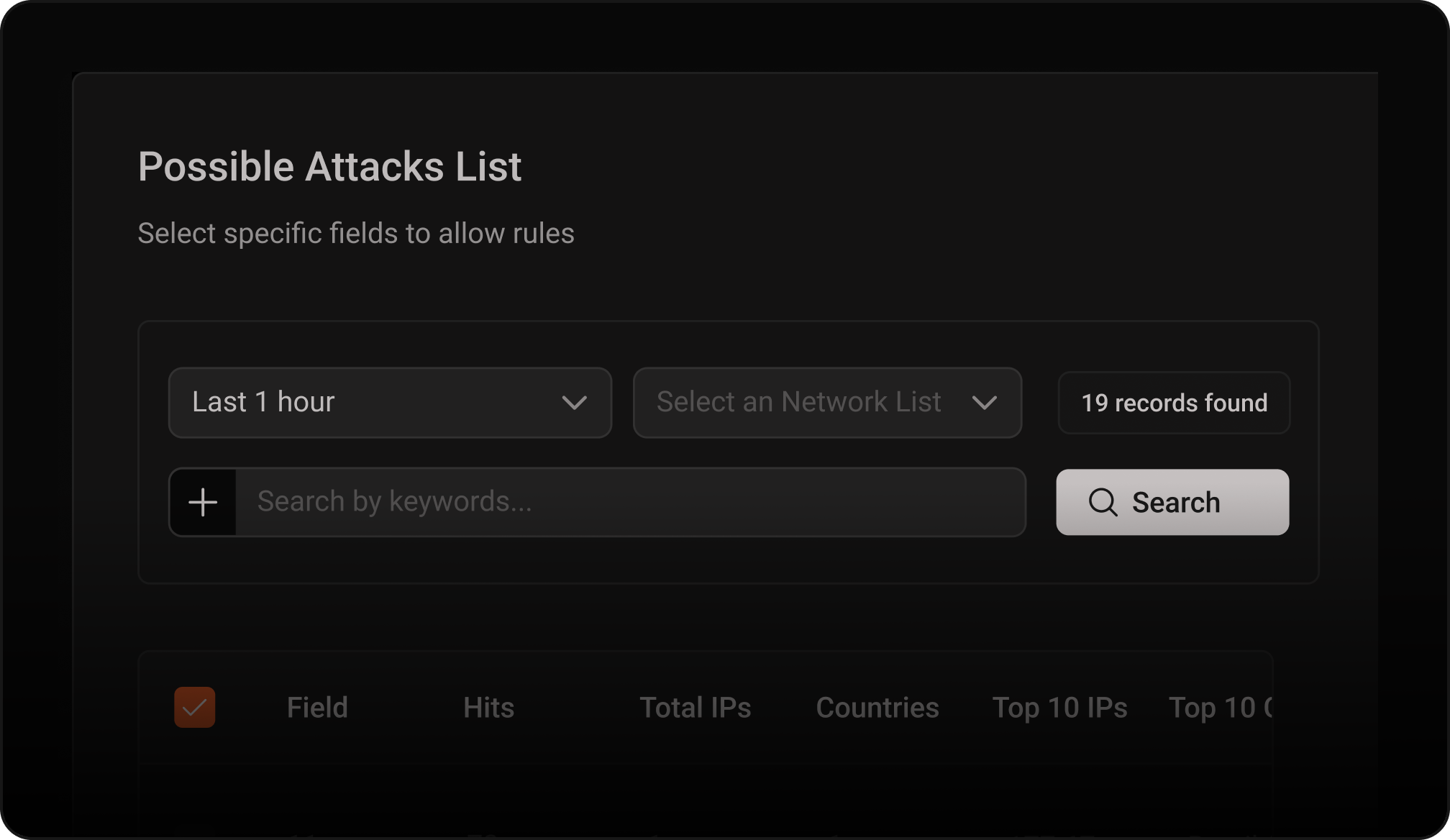
Azion's unified security platform—combining WAF, Bot Manager, and Network Shield—prevents a comprehensive range of attacks including SQL injection, cross-site scripting (XSS), XML external entities (XXE), remote file inclusion (RFI), local file inclusion (LFI), command injection, path traversal, cross-site request forgery (CSRF), server-side request forgery (SSRF), unsafe redirects, and zero-day exploits. For APIs, Azion WAF defends against injection attacks, broken object-level authorization (BOLA), excessive data exposure in requests, lack of rate limiting, broken function-level authorization (BFLA), unrestricted resource consumption, and server-side request forgery (SSRF). Bot Manager handles credential stuffing, scraping, and automation abuse. Network Shield provides network-layer DDoS protection. Our risk scoring detects both known attack signatures and anomalous behavior patterns.
How much does a web application firewall cost?
Azion WAF uses transparent usage-based pricing where you only pay for requests analyzed by the WAF. Start with $300 in free credits to test the service with no credit card required. Pricing scales with your traffic volume, with no hidden fees, infrastructure costs, or vendor lock-in. Our distributed architecture eliminates the need for centralized cloud infrastructure, reducing costs and latency. Enterprise plans include custom rule development, dedicated support, and volume discounts. Most customers save 30-60% compared to traditional enterprise WAF solutions while eliminating infrastructure management costs entirely.See more
Do I need a WAF if I already have a CDN or load balancer?
Yes, CDNs and load balancers do not provide application-layer security against web attacks. While CDNs optimize content delivery and load balancers distribute traffic, they cannot detect or block SQL injection, XSS, or other OWASP Top 10 threats. Azion WAF integrates directly with our CDN and distributed platform, providing comprehensive security without adding latency. You get both performance optimization and enterprise-grade protection in a single platform, with security events analyzed before requests reach your origin servers.
Nativelly Protected.Always.
Talk to our team of experts and start saving money